Substitution Ciphers
This section undergoing review and edits for clarity
The Basics
The basic substation cipher is a type of simple mono-alphabetic cipher. One example would be the Ceaser Cipher (A=C, B=D, .. Z=B). These are known as shift, or rotational (ROT), ciphers. All things considered these are not terribly secure and are easy pickings for cracking with basic frequency analysis.
ABCDEFGHIJKLMNOPQRSTUVWXYZ
--------------------------
EFGHIJKLMNOPQRSTUVWXYZABCD
ATLANTIA = EXPERXME
The obvious next step in the evolution of the mono-alphabetic cipher is the randomization of the letter order (I should put a reference here). In this variant any give letter could be any other given letter, assuming that letter has not already been used. Since the order of the letters matters (consistency) we are working with permutations. Knowing that the number of permutations can be calculated thusly: P(n,r)=n! / (n−r)! In this case we have 26 elements, n, and we're deriving a set of all 26, r. This gives us approximately 4.03E+24 different cipher sets to work with. This gives us a bit better security but is again easily broken with simple cryptanalysis.
ABCDEFGHIJKLMNOPQRSTUVWXYZ
--------------------------
ASYKRWUBHEQMICDTFPGJXNLOVZ
ATLANTIA = AJMACJHA
Affine Ciphers
OK. Now let's introduce a mathematical key to quickly generate our ciphers. Remember that 4.03E+24 number? Well, if we only ever used one cipher then it would essentially defeat the purpose of having cipher flexibility. On the other hand, if we put 52 ciphers on a page it would take 7.75e+22 pages of paper. If you used both sides of the page you can get that down to a svelte 3.875e+22 pages. Knowing that you get about 150 pages per height inch we have a stack 2.5833333e+20 inches tall. That's 2.1527778e+19 feet, or 4.0772306e+15 miles high. For frame of reference, the Milky Way Galaxy is a mere 5.879e+17 miles across. Basically, you're not getting that book on your desk.
MATH to the rescue!
We can encipher the entire alphabet by introducing a couple seed values and then getting the remainder of the operation based
on the width of our character set. This is known as the Affine Cipher.
Simply select two seed values, n and r, We'll use 5 and 10 for an example, and plug them into the equation.
It's important to point out that since we're using the modulus of set a seed values that we will produce a mono-alphabetic system.
f(m) = (nm + r) (mod 26) f(m) = (5m + 10) (mod 26) A = 1 B = 2 O = 15 f(1) = (5*1 + 10) (mod 26) f(1) = (15) (mod 26) f(1) = 15 f(2) = (5*2 + 10) (mod 26) f(2) = (20) (mod 26) f(2) = 20 f(15) = (15*2 + 10) (mod 26) f(15) = (40) (mod 26) f(15) = 14 A = O B = T O = N ...
Mary's Cipher
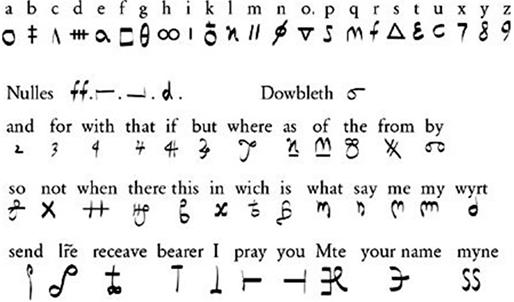
This key pretty much sums it up but I'll get back here and add some history and an example or two. Feel free to try the translator
and build your own secret messages using this period cipher! This key is taken from Simon Singh's site (http://simonsingh.net/The_Black_Chamber/maryqueenofscots.html)
and is based upon material found in his book, The Code Book (Singh, 1999). I highly recommend his site.
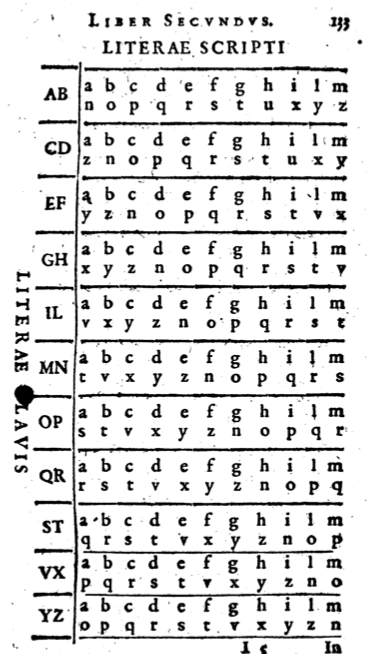
Porta's Parity - polyalphabetic
Porta actually kinda ripped off Bellaso here... or at least didn't give proper credit. That said, Porta did fully explain the following system of a key dependent polyalphabetic system. In Porta'a De Occultis literarum Notis (1606 reprint) we are presented with many, many, substitution ciphers. For this substitution cipher we select the plaintext letter from the KEY column on the left. Then you locate the letter that you want to encode and use the letter directly adjacent to it. Notice that each pair of letters on the left has its own ciphertext on the right. Short, sweet, pretty ingenious. For example, to encode 'atlantia' with the key of 'code' we go to the C/D row first a is opposit z so here Z=A. Then we go to the o row and find that B=T, and so on. Atlantia is thusly enciphered as ZBXYBBUY. Decoding is just as simple, assuming you have the key word :-)